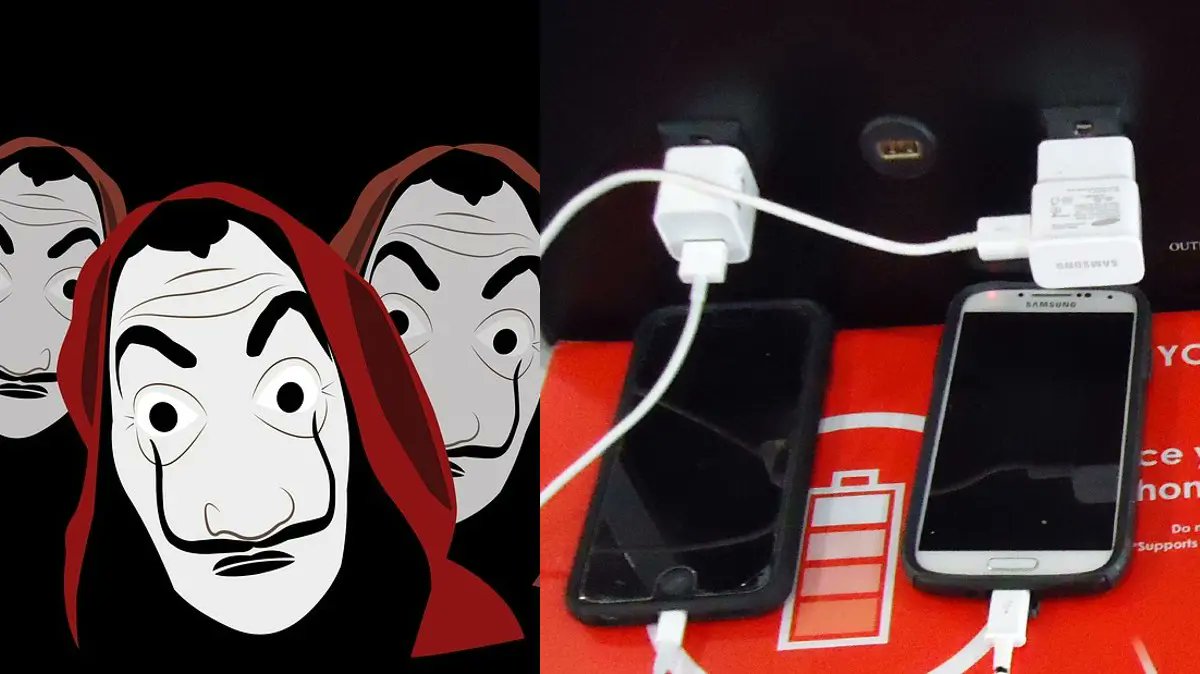
Avoid Public Phone Charger. We’ve all been there: stuck in an airport terminal with a dying phone and no access to an outlet. Public USB charging stations seem like a godsend in those moments, offering a quick and convenient way to get back online.
But hold your horses! The Indian government’s recent warning about the USB charger scam highlights a hidden danger lurking behind those seemingly helpful ports.
The Threat: Juice Jacking and Your Vulnerable Data
The USB charger scam, also known as juice jacking, involves cybercriminals tampering with public charging stations. When you plug your phone in, instead of just receiving power, your device might establish a data connection with the compromised port. This opens a backdoor for hackers to:
- Install Malware: Malicious software can be downloaded onto your phone silently, potentially stealing your personal information like contacts, photos, messages, and even financial details. These programs can also lock you out of your device and demand a ransom to regain access.
- Steal Data Directly: Hackers can exploit the data connection to directly access sensitive information on your phone. This could include everything from your browsing history and social media logins to your banking credentials and work documents.
Why Public Phone Charger Are Vulnerable
Public USB charging stations are often located in high-traffic areas like airports, train stations, cafes, and shopping malls. This makes them easy targets for criminals to tamper with. The tampering itself can be done in several ways, some more sophisticated than others:
- Hardware Modifications: In some cases, hackers might physically modify the charging station’s internal hardware to install malware or data-stealing software.
- Infected Charging Cables: Malicious actors might replace the original cables with ones programmed to steal data or install malware.
- “Juice Jacking” Devices: Criminals can insert small devices between the charging station and the cable, creating a bridge for data transfer while still supplying power to your phone.
The Risks Go Beyond Data Theft
While data theft is the primary concern, juice jacking can also pose physical risks:
- Damaged Devices: Tampered ports might deliver an unregulated surge of power, potentially damaging your phone’s internal components.
- Spyware Installation: Hackers could install spyware that allows them to monitor your phone’s activity, including calls, messages, and even camera usage.
Staying Safe: Power Up with Confidence
The good news is that you don’t have to completely avoid public charging stations. By following these steps, you can significantly reduce the risk of falling victim to juice jacking:
- Pack Your Power: This is the golden rule. Invest in a good quality portable charger or power bank. They’re readily available, come in various capacities, and can keep your phone juiced up throughout the day.
- Only Use Trusted Sources: If you absolutely must use a public charging station, prioritize safety over convenience. Look for stations located in well-maintained, well-lit areas with CCTV surveillance. Avoid using stations in deserted areas or those that look damaged.
- Embrace “Charge-Only” Cables: These specially designed cables only allow power to flow to your device, preventing any data transfer. While not as common as regular charging cables, they are readily available online and at some electronics stores.
- Power Down for Safety: Consider turning off your phone or putting it in airplane mode while charging at a public station. This reduces the risk of malware installation or data theft even further.
- Be Security Savvy: Keep your phone’s software and apps updated with the latest security patches. This helps close vulnerabilities that hackers might exploit. Utilize strong passwords and PINs for your phone and consider enabling two-factor authentication for added security.
- Monitor Your Phone: Don’t leave your phone unattended while it’s charging in a public place. Stay vigilant and unplug it if you notice anything suspicious with the charging process or the station itself.
- Consider Third-Party Solutions: Some companies offer portable chargers with built-in data blocking technology, offering an extra layer of security. While not as common yet, these options might become more readily available in the future.
Beyond Public Charging: Securing Your Phone on the Go
Staying safe extends beyond public charging stations. Here are some additional tips to keep your phone secure when you’re out and about:
- Beware of Unsecured Wi-Fi: Avoid using public Wi-Fi networks for sensitive tasks like online banking or accessing personal accounts. If you must use public Wi-Fi, consider using a Virtual Private Network (VPN) to encrypt your data traffic.
- Bluetooth Blues: Be cautious when connecting to unknown Bluetooth devices. Hackers can exploit Bluetooth connections to steal data or install malware.
-
App Scrutiny: Only download apps from trusted sources like official app stores (Google Play Store or Apple App Store). Read app reviews and permissions carefully before installing them. Don’t grant unnecessary access to apps, especially those requesting microphone, camera, or location permissions when not strictly relevant to the app’s function.
-
Phishing Finesse: Be wary of suspicious text messages or emails, even if they appear to be from legitimate sources like banks or social media platforms. Don’t click on any links or attachments within these messages, and never enter your personal information through such prompts.
-
Physical Security: Always keep your phone in a secure place like a zipped pocket or a phone holster. Don’t leave your phone unattended in public spaces, even for a short while. Consider enabling features like “Find My Phone” or “Find My Device” offered by your phone’s operating system. These allow you to locate your phone remotely if it’s lost or stolen, and even enable data wiping as a last resort.
-
Back It Up: Regularly back up your phone’s data to the cloud or an external storage device. This ensures you don’t lose precious photos, contacts, and documents even if your phone is compromised or damaged.
-
Education is Key: Talk to friends and family about the dangers of juice jacking and other mobile security threats. By raising awareness, we can create a safer mobile environment for everyone.
By following these comprehensive strategies, you can transform your phone from a potential security vulnerability into a secure and reliable tool, no matter where your travels take you.
Remember, a little caution goes a long way in protecting your information and maintaining peace of mind. Stay charged, stay safe, and stay informed!
Please share your thoughts in comment about , at theproductrecap.com we are open to friendly suggestions and helpful inputs to keep awareness at peak.